Install MySQL In Ubuntu On VMware And Connect Through The Host Pc (windows or any host pc)
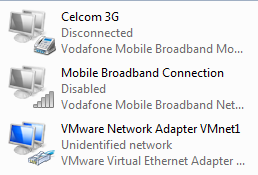
This article explain how to install MySql 5.5 with Ubuntu 12.04 on VMware (VMware Workstation 8.0.1) and connect through the virtual pc to access the MySql databases in Host pc (Windows or what ever os on host pc). 1.Install MYSQL On Ubuntu 12.04 sudo apt-get install mysql-server (make sure you are log in as root user,fast internet connection help to download package's correctly.if network connection slow,then download packages may be corrupted!) 2.Install MYSQL Workbench sudo apt-get install mysql-workbench